Sonardyne has released the following article about the company’s work with the UK Ministry of Defence’s Defence Science and Technology Laboratory (Dstl) to develop a new standard for secure waveforms in underwater communications. The new standard will enable allied navies to interoperate systems such as AUVs (autonomous underwater vehicles) and other unmanned underwater vehicles (UUVs).
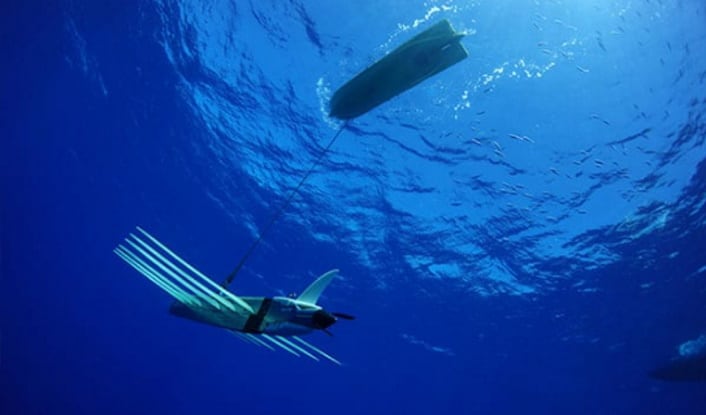
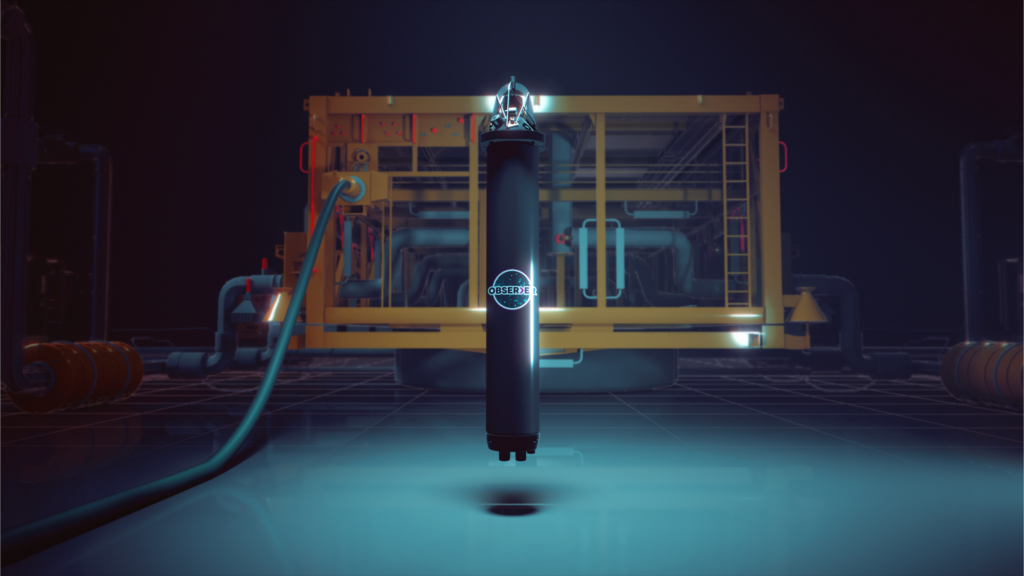
The 21st century battlespace is complex. It’s multi-domain, it’s multi-threat and it’s not always obvious open, armed conflict. The underwater battlespace embodies all of these challenges to an increasingly significant degree. It’s a space that’s pivotal to protecting critical national infrastructure and safeguarding maritime trade. But it’s also a challenging place to operate, whether that’s in intelligence, surveillance and reconnaissance, mine hunting capability or command and control. It’s also a space where the threats are proliferating, from advances in antisubmarine warfare through to asymmetric actors, crewed, uncrewed, small and autonomous.
Working between all these actors – be it different platforms, domains and nations – in the underwater theatre is an even bigger challenge. It requires interoperability and that means the need for assets across domains and nations to talk to each other. A new standard in underwater communications is needed to meet these needs.
Sonardyne has been leading a technical programme to develop a high-integrity secure waveform for acoustic communications, set up in response to a Defence Science and Technology Laboratory (Dstl) requirement. The work, funded by the UK Ministry of Defence, via Dstl, and primed by Thales UK, seeks to develop Phorcys, an open standard for secure acoustic communications that will enable navies to collaborate and interoperate, assuring secure transmissions and communications. Alexander Hamilton, Principal Communications Scientist at Dstl, and Ioseba Tena, Head of Defence at Sonardyne, discussed what this means.
Supporting Anti-Submarine Operations
“One of the big problems at the moment is interoperability,” says Hamilton. “There needs to be a secure, high-performance protocol for anyone and everyone to use. We need secure, interoperable communications to underpin command, control and communications, to do mine countermeasures and mine hunting, to support anti-submarine operations.
“Underwater communications is a critical enabler, to take an example it’s key to enable things like the Future Commando Force advanced autonomous force. We need to work collaboratively, to achieve interoperability between the UK and its allies, but also multi-domain integration of underwater assets where they are able to connect to a wider mission network. But to enable all this we need the underwater battlespace to have secure, resilient, underwater communications.”
Tena says, “We already have open standards, take for instance JANUS. This was designed as the first interoperable protocol; the first step towards interoperability. I guess the missing ingredient with JANUS and other standards has been security.”
Secure and Resilient Underwater Communications
Hamilton explains, “Yes. That’s right. The difference is having a secure and reliable protocol stack and there’s a difference between resilience and security. Security is about having confidentiality, integrity and availability. Resilience speaks to integrity and availability, but doesn’t necessarily provide that confidentiality.
“Traditional acoustic communications in the commercial domain are resilient, with high availability and high performance, but while commercial-off-the-shelf systems allow interoperability, they result in vendor lock-in. Furthermore, they’re also not inherently secure. And while existing protocol stacks can have security added on, AES-256 encryption for example has been applied to JANUS, this adds overheads and is outside of the protocol stack. It’s not a secure by design approach. We want to have high performance communications to support fast information transfer across the underwater battlespace. We also need security.”
Introducing Phorcys
“It’s the development of a high-performance protocol stack that will be available as an unclassified (non-protectively marked) standard,” says Hamilton. “It’s a secure-by-design approach using cryptographic keys, not just security by obscurity. We’re working with the National Cyber Security Centre (NCSC) on that to ensure security of these communications is approved to government standards. Adhering to the standard will allow for multi-domain integration across different assets, interoperability between different nations, platforms and areas within the navy. That’s because, by using cryptographic keying approaches, unless you have the key, you can’t get access to the network and you maintain the security of your communications. A third party wouldn’t be able to understand the content of what was being transmitted.
Tena points out, “Cryptographic keys also accommodate different levels of interoperability. A UK platform with UK codes will only communicate securely with another UK platform with UK codes. A UK platform could also have NATO codes, to communicate with a NATO platform, or a US platform might have NATO codes, etc. “
“That’s the aim. In fact, the standard will be unclassified; it’s the key that defines which users have access to the information. That means there can also be a zero code that’s open to all.” Hamilton explains.
Situational Awareness – Recognising Friend From Foe
“Going forward, an important part of Phorcys will also be about enabling situation awareness between these underwater assets; being able to challenge and recognise friend from foe. In the future, during an operation in a busy seaway, it will become increasingly important to recognise your autonomous vehicle returning to a mother ship from an incoming autonomous torpedo.”
As part of the Phorcys programme, Sonardyne experts are collaborating with Newcastle University to design a waveform capable of working across different frequency bands in order to target all environments, from confined spaces to deep, open waters.
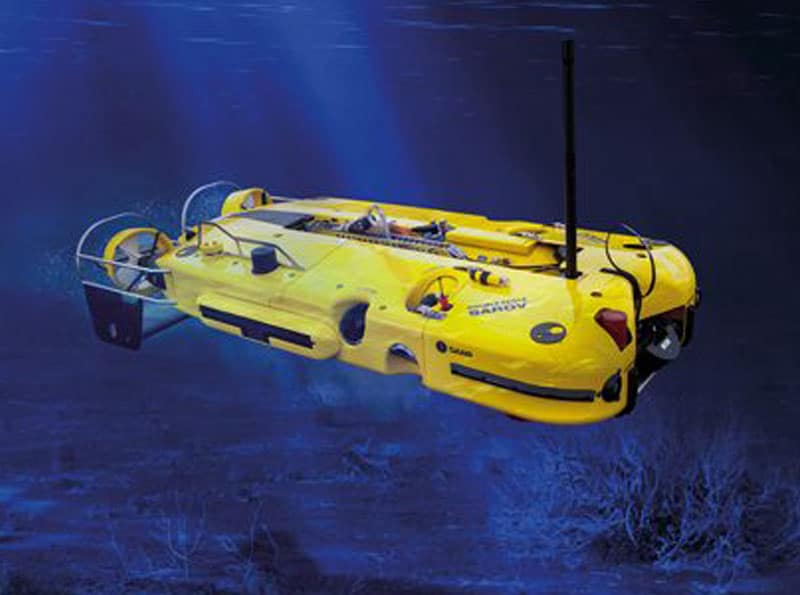
“Phorcys is exciting because it will allow for interoperability between different platforms across the entire underwater battlespace as it will operate at different frequency bands,” says Hamilton. “If you want longer range, you might use lower frequencies. For small unmanned underwater vehicles (UUV) operations, you might want to use one of the frequency bands at 20 to 28 kHz. It allows you to control UUVs with higher degree of fidelity. It allows you to get more data back, and provides assured command and control across your assets and fast data transfer. Because it’s being developed as a standard, there will be lower cost of development and a shorter time to deploy,” says Hamilton.
Open, Interoperable Standards
So what are Sonardyne’s plans for the technology? “Sonardyne intends to implement this standard and work with third parties to promote its use,” says Tena. Our aim, on completion of this project, will be to continue to offer our customers our commercial-off-the-shelf solutions, built on our commercially leading and robust Wideband digital signal heritage and expertise, as well as the opportunity to work with secure Phorcys waveforms using the same hardware platforms.
“We want vendor buy-in, not vendor lock-in. It will simplify procurement, because vendor systems that comply to the standard can be used together and there’s still space for companies to compete,” says Hamilton. “It opens up a different market space; it opens up competition on hardware and processing, optimising size, weight and power, for small UUVs, for example.
“It will also open up innovation higher up the protocol stack, in swarm autonomy behaviours, for example. Rather than being focused on communications, developers can focus on application and platform integration, layer processing, autonomy and graphic user interfaces into the network.
“Because the protocol will be unclassified, the work we’re doing will also be available to other industries to use. The oil and gas industry, for example, could use it as part of their underwater robotics operations, ensuring the security of their data.”