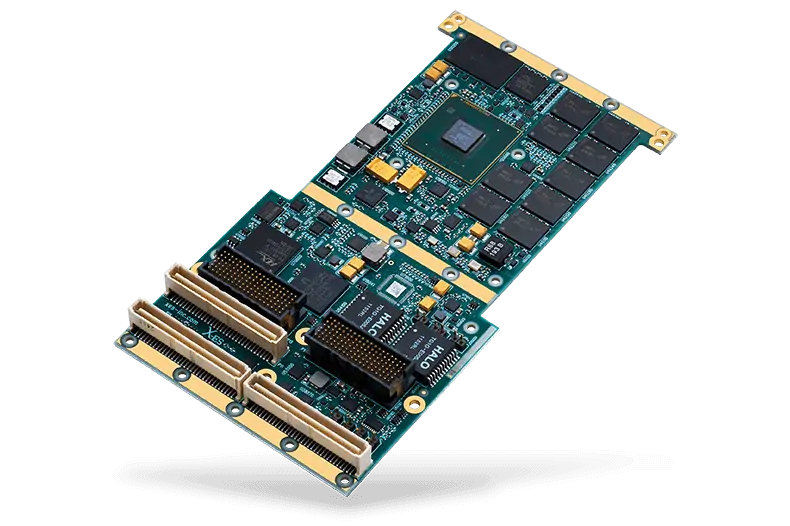
Extreme Engineering Solutions (X-ES) has announced the availability of the company’s new NXP QorIQ T2081 processor-based COTS board solution, the XPedite6101, with a certification-ready multi-core operating system environment, Wind River VxWorks 653 3.0 Multi-core Edition platform. In addition to being fully ARINC 653-compliant, this solution is integrated with Wind River’s Information Assurance Framework (IAF) to support secure booting for applications requiring enhanced levels of security.
The Wind River VxWorks 653 platform enables avionics vendors and hosted-function suppliers to independently develop and deploy multiple applications on a single multi-core hardware platform, supporting rigorous avionics safety standards. These supported standards include RTCA DO-178C for certifying compliance with the applicable airworthiness regulations for the software aspects of airborne systems and equipment, and ARINC 653 for space and time partitioning in safety-critical avionics real-time operating systems (RTOS).
The VxWorks 653 multi-core scheduler enables multiple guest operating systems on a shared compute platform, allowing applications to run in parallel in order to increase compute capacity. In addition, this platform provides fault containment, high portability for lower upgrade costs, reduced development costs with a development suite based on Eclipse, and reduced RTCA DO-178C platform certification time supported by commercial-off-the-shelf (COTS) certification evidence.
The enhanced security of this solution is derived from the integration of Wind River’s IAF. The IAF utilizes the PowerPC/NXP Trust Architecture, known as the QorIQ Platform Trust Architecture, to enable secure boot, including a built-in security engine that can hide a One Time Programmable Master Key (OTPMK) in a write-only register. This security engine is ideal for performing cryptographic offload of hashing, encryption, and decryption.
The foundation of the safety and security capabilities of this platform is the VxWorks 653 BSP. This BSP is fully integrated into the trusted boot sequence and is controlled by the IAF, and supports the following capabilities:
- Four (4) physical cores (threading not supported)
- Serial ports
- ECC support
- I2C support (GPIO, TMP102 Ambient Temperature Sensor, ATD6641A Dual Temperature Sensor, AT24CM01 SEEPROM, M41T00 Real-Time Clock)
- DDR SDRAM: 8 GB board total; 2 GB accessible using VxWorks 653 Multi-core Edition, version 3.0.1.1
- PCIe – PCIe controller #1, #3, and #4 on the T2081
- Ethernet: Both MEMAC interfaces on the XPedite6101 (MEMAC2 and MEMAC3)
- 4 GB NAND Flash is supported via the CERT HRFS, NAND FTL, MTD, and IFC NAND driver
- Boot from NAND flash (using U-Boot)
The XPedite6101 supports multiple NXP QorIQ processor configurations, a number of I/O ports including Gigabit Ethernet, serial, USB, and SATA, and up to 8 GB of DDR3-1600 ECC SDRAM. When configured to use the T2081 processor, the XPedite6101 maximizes performance with eight virtual (four dual-threaded) Power Architecture e6500 cores running at up to 1.8 GHz.
The Wind River VxWorks 653 software platform was specifically developed to comply with rigorous avionics safety standards. The XPedite6101 offers a suitable hardware platform for VxWorks 653 by providing a size, weight, and power (SWaP) optimized computing solution that is ideal for the needs of the military and aerospace industry, including development of unmanned aircraft systems (UAS) and other unmanned vehicles.
The XPedite6101 implements secure boot through NXP’s Trust Architecture systems to enable more secure and reliable applications. The joint solution’s secure boot technologies prevent the CPU from running untrusted code, detect and reject security violations, and prevent the extraction of sensitive data from an application.
“NXP is pleased that X-ES’ XPedite6101 is using our T2081 processor in a solution with the reliability needed by avionics customers,” said Toby Foster, Senior Product Marketing Manager, NXP Digital Networking. “NXP’s T-series processors are characterized by high performance and low power, making them a great choice for demanding but highly constrained avionics applications,” Foster commented further. “Besides the inherent trusted security features built into NXP processors, X-ES leverages the T2081’s high level of I/O integration for impressive performance density.”
Wind River’s secure boot technology creates an extra layer of security for QorIQ processors by performing a hardware check on software in the boot sequence. All code included in the VxWorks 653platform BSP is digitally signed and includes a tightly controlled RSA public and private key pair. Before allowing an application to boot, secure boot checks the application’s software against the private signature key. In the event that an unsigned kernel is discovered, the secure boot technology prevents the compromised system from booting, thereby preventing data extraction.